How to defend against cloud misconfigurations, vulnerabilities and insider threats
Authored by Milad Aslaner of SentinelOne and Gwenn Cujdik of AXA XL
Over the last decade, Microsoft has expanded its product portfolio from an operating system provider to a company providing various solutions spanning productivity, collaboration, and cloud capabilities. Some organizations today choose Microsoft 365 and Microsoft Azure to consolidate their vendor portfolio while often compromising on best-in-class capabilities. This approach has introduced significant risks to organizations as they become overly dependent on a single vendor.
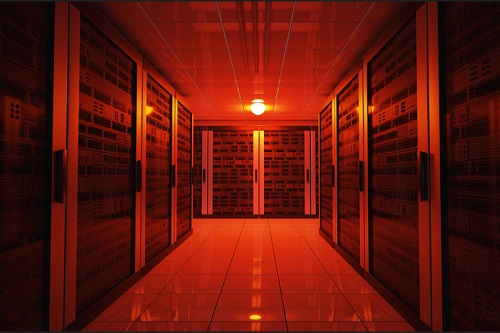
Today, all Microsoft services are dependent on Azure Active Directory as its primary Identity and Access Management (IAM) solution. With that, the weakest link in a Microsoft environment has become the user identity. When a threat actor can compromise a user identity with elevated privileges like the security administrator role, they can evade all the defense measurements and security tools of Microsoft. In this article, we will look into how to identify and defend against some common cloud vulnerabilities, insider threats, and dangerous cloud misconfigurations.
About AXA XL
AXA XL is the P&C and specialty risk division of AXA which provides property, casualty, professional and speciality products to industrial, commercial and professional firms, insurance companies and other enterprises, here in the UK and throughout the world. With underwriting teams based in the US, UK, EMEA and Asia Pacific regions, we can make decisions close to the markets you serve and work with you to tailor cover to your business needs.
We help businesses adapt and thrive amidst change. Rather than just paying covered claims when things go wrong, we go beyond protection into prevention so your business can go beyond the unexpected.

