Private school fee payments from parents are currently one of the top targets for cyber criminals, especially with invoices for next term being issued over the current weeks, warns Cyber Decider.
Schools generally, and private school fee payments particularly, are currently popular with cyber criminals because of the combination of them being large (generally £4,000-£10,000 per term) and poor cyber security at many schools makes for an easy target for hackers. Neil Hare-Brown, the CEO of Cyber Decider says: “In 2017 we saw schools generally become a big target for cybercriminals. Their security is often poor, and their fees administration largely undertaken out of their electronic mailbox which is often hosted online, making it easy to hijack.
“In addition, the parents with whom they communicate generally use webmail, and often from insecure systems. Families and schools are sharing lots of information about payments for fees, trips and everything else, so these mailboxes hold lots of important personal data such as bank and credit card details, passport images, medical and family information. Many schools have moved their email systems online and use payment gateways, but often they use systems that are insecure.
“Also, school staff and parents are easily deceived, and scams operated over the holiday period when schools are closed, mean the alert won’t be raised quickly. This gives the criminals time to transfer funds with little chance of them returned.
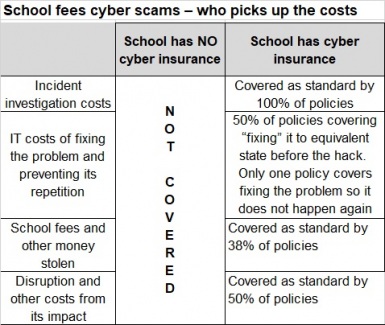
“The big problem is “who picks up the bill”, especially for the stolen school fees. Many schools don’t have cyber insurance, but even those with policies should check them carefully as many cyber insurance policies will not cover the money stolen.
“For instance, several insurers only cover this under a crime policy – the cyber policy will only cover theft of data and not theft of money. Even where the cyber policy does cover theft of the money, there may be a sub-limit or restrictions on cover such as an exclusion for “social engineering” losses (i.e. where parents are tricked into sending the money to a dummy account).
“In many there will only be cover for the forensic, legal or PR costs associated with the theft of data from the school, not the potentially huge cost of successful scams against parents. Schools do need to check their policy carefully to ensure they are clear on what costs they are covered for… in advance of needing to claim.”
How the scam typically works:
- Parents receive an email giving them payment details for the school fees, perhaps saying these have changed.
- However, hackers have surreptitiously gained access to the school’s email, usually through an undiscovered phishing attack and in fact the payments will go into hacker’s account. They also set up automatic rules so responses from parents requesting confirmation of authenticity get diverted to the hackers, so the school does not see them.
- Parents make payments to the hacker’s bank account, which is emptied early in the next term, netting the criminals sometimes tens and often hundreds of thousands from a single school. From each single attack perspective, the amounts stolen are not high enough to warrant a full police investigation! Most fraudsters disappear without a trace and elude prosecution.
- Other details gained - such as personal details of staff, children and parents - are then either sold to other cybercriminals using sites on the “Dark Web” for identity frauds, or used for this purpose by the original hackers later on.
What are the costs when school fees are stolen?
When such a scam operates, the typical costs are:
- The incident investigation costs including the need for specialist digital forensics, legal and PR advice.
- The accountancy costs of sorting out what was stolen and when and what wasn’t.
- The IT costs of ensuring the systems are no longer vulnerable.
- The lost school fees will fall on the school in many cases and, in others, parents (see table below).
- The costs of disruption, diversion of manpower and management time over the many weeks needed for resolution, as well as the loss of goodwill and reputation amongst parents and others affected.
How to stop such scams – advice for schools and parents
Action for parents:
If you get payment requests from schools or anyone by email, especially one changing the previous arrangements, be very aware! Telephone the school on its normal number, don’t email them, and double-check verbally with the school before making the payment.
Actions for schools include:
- All organisations taking payments, especially schools, should have suitable cyber security measures in-place and to consider cyber insurance to provide cover for the costs of investigation, notification, compensation, remediation, theft of money and follow-on crimes.
- Thorough and regular cyber security training for all staff, and ensure procedures are followed.
- Avoid using generic mailbox accounts and do not perform school administration entirely ‘from the mailbox’.
- Use a payment gateway for payments, but make sure it is thoroughly tested to ensure security.
- Use a secure communications portal for use in communications with parents in all matters, including school fees.
- Ensure two-step authentication is implemented on all online systems in use by the school.

